CloudShark Brings Wireshark to the Web
By stretch | Tuesday, June 22, 2010 at 1:34 a.m. UTC
If you've browsed through the packet captures available on this site recently, you may have noticed a new link next to the download link for each: "view online." Thanks to the remarkable work of a company called QA Cafe, you can now view packet captures online via a new free service dubbed CloudShark. Their (short and friendly) press release is here.
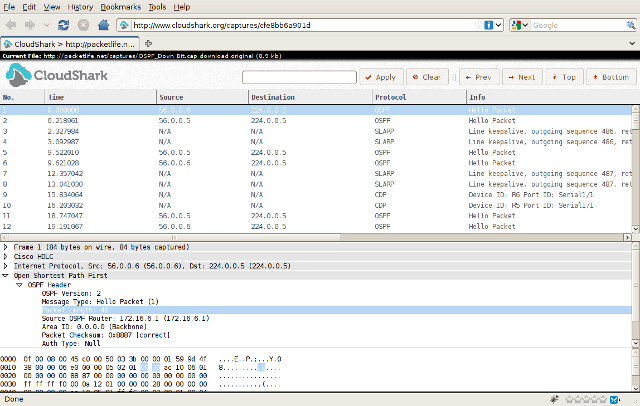
CloudShark is essentially a lightweight mock-up of the Wireshark packet analysis interface ported to be completely web-based. To open a capture file in CloudShark, you can upload it directly, reference it by URL, or email it. Here's an example using the capture from last week's TCP Selective Acknowledgments (SACK) blog post.
CloudShark's interface is very slick, and mimicks very closely the behavior of Wireshark. For example, you can expand and select individual headers and fields within each packet in the second pane. As in Wireshark, selecting a particular field should highlight the corresponding raw data in the third pane (this may not be working on all browsers but I can confirm it works with Firefox 3.6). Cloudshark even supports display filtering.
The CloudShark FAQ explains that the analysis is actually wrapped around tshark, a console utility which belongs to the Wireshark family. This is already a rather impressive project, and I'm curious how it might grow from here.
Posted in Resources
Comments
June 22, 2010 at 3:23 a.m. UTC
Parsing untrusted pcap files, with Wireshark especially, seems like a bad idea.. Hope you fixed all of those vulns!
June 22, 2010 at 9:15 a.m. UTC
pcapr.net does the same thing, IMHO in a more collaborative way, but is limited to most common datalink types, while cloudshark seems to be crunching much more captures... good :)
June 22, 2010 at 9:44 a.m. UTC
Impressive indeed. It definitely has strong potential. Thanks for sharing.
June 22, 2010 at 12:29 p.m. UTC
Too bad these guys didn't pipe up a couple of weeks ago. Last week was SharkFest '10, they could have got a lot of exposure there.
Sean
June 22, 2010 at 2:54 p.m. UTC
to bad it's not secure as most of my caps I don't want just anyone to see :-(
June 22, 2010 at 3:07 p.m. UTC
@jduck: I'm not sure if your comment was toward me or the maintainers of CloudShark. I can't speak for them, but as for the capture library on Packet Life, I review every submitted capture offline and must approve it before it is subjected to tshark on the back end for parsing.
June 22, 2010 at 6:35 p.m. UTC
really thrilling
regards
Shivlu Jain
http://www.mplsvpn.info
June 22, 2010 at 9:32 p.m. UTC
Very nice. This has a lot of potential. Hoping to see this actively developed and maintained! seems like a great project.
June 23, 2010 at 6:33 p.m. UTC
Hmm I got all excited about it, so I went to try it with a random capture off my desktop and got:
(Request too large)
on my first attempt. Moving back into the 'meh' category for now...for one it takes like 30 seconds to install wireshark, but I suppose the collaboration is a good idea. Next time I'm dealing with TAC or something it could be useful so long as it's a small capture... beats email!
June 24, 2010 at 1:38 p.m. UTC
@Nick: They have a capture size limit of 512 KB, for now anyway.
June 24, 2010 at 5:32 p.m. UTC
@stretch: Sorry, yes it was more for CloudShark... I guess I got disoriented hehe.
July 3, 2010 at 2:37 p.m. UTC
Nice first step.
Let me present food for thought.
Cloudshark service gives the ability to be HTTP(s) proxy.
The proxy decodes the stream between the user and a web server. Any user/any web server (as a NOC you can tell the user to point proxy in a browser easy enough)