Free route monitoring service by BGPmon
By stretch | Wednesday, October 15, 2008 at 4:37 a.m. UTC
BGP prefix hijacking has been perceived as a growing threat over the last year or so. A prefix hijacking occurs when an unauthorized party advertises one or more prefixes belonging to another party. By advertising the prefixes with more favorable characteristics (such as longer matches or a shorter AS path), traffic across the Internet can be redirected for malicious purposes, effectively creating a man-in-the-middle attack with global reach.
The highest-profile example of such a scenario occurred last February when Pakistan Telecom, in an effort to block access to YouTube.com from the entire country, accidentally advertised to the Internet a "black hole" route for YouTube's public address space. All (or most) traffic destined for YouTube.com was being routed to Pakistan, where it was subsequently discarded. Needless to say, some people got pissed.
Incidents such as this have prompted much discussion, but currently this vulnerability still persists throughout the Internet. In the absence of a solution, more attention is being paid to monitoring BGP advertisements. Organizations and individuals have been writing code to leverage the insight of public looking glasses and automate the monitoring of address prefixes.
One such service recently debuted at BGPmon.net, managed by Andree Toonk. BGPmon provides free monitoring of select BGP prefixes and automated E-mail notification when suspicious changes are observed. For example, assume your AS 123 normally advertises 204.32.0.0/16 to the Internet. If AS 456 begins advertising two routes, 204.32.0.0/17 and 204.32.128.0/17, traffic will follow these more-specific routes to AS 456. BGPmon would detect this as a possible MITM attack and alert the administrators of AS 123.
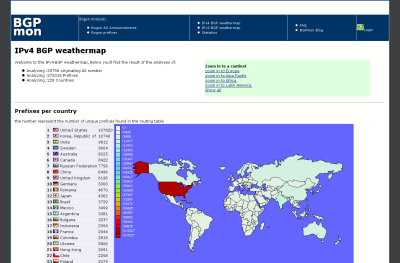
BGPmon also provides some interesting weathermaps and general statistics of the global routing table. Even if you don't administer an autonomous system, the ongoing growth and reshaping of the world's routing table can be fascinating to observe.
Posted in Resources
Comments
October 16, 2008 at 1:31 a.m. UTC
Oooo that is interesting.
October 16, 2008 at 11:08 p.m. UTC
very informative. keep up the good work
October 20, 2008 at 6:25 a.m. UTC
Nice article, but ISP's are ultimately responsible for what they advertise and who they peer with, If a ISP (exluding Pakistan Telecom) has proper policies in place, this risk is reduced greatly.
October 20, 2008 at 11:15 p.m. UTC
Hi Ruhann, yes you are correct. However, we all know that by far not everyone does proper filtering. And even if they do, it's easy to add a route to a IRR/whois database so that your upstream (like Level3, or others who use IRR for filters) will accept it anyways. This was how the guys at defcon (Stealing the Internet) did it. So yep, good filtering for sure important, but unfortunately today we are not there yet and we'll need tools like this!
July 21, 2009 at 10:07 a.m. UTC
tks for the effort you put in here I appreciate it!
May 15, 2012 at 11:14 p.m. UTC
This is also very interesting tool: http://www.ris.ripe.net/bgpviz/